This section describes how to configure the SFTP listener.
The following table lists and describes the procedure for the SFTP Listener.
|
Property Name |
Property Description |
|---|---|
|
Host Name (required) |
The name of host machine where listener contacts the service to obtain requests from. |
|
Remote Port (required) |
The port to connect to on the SFTP site, blank for default port 22 |
|
Input Path |
The directory with optional pattern on SFTP host from which to retrieve files. A specific file name or DOS-style pattern) can be used. Do not use suffix in. |
|
Include Symbolic Links (required) |
If set to true, then the SFTP listener processes the symbolic links. |
|
Include Hidden Files (required) |
If set to true, then the SFTP listener processes the hidden files. |
|
Destination Directory |
The directory on SFTP host to return responses to. |
|
Data, Signal or Streaming (required) |
Determines how the input will be processed by the SFTP listener. Select one of the following options from the drop-down list:
|
|
Local Store Directory |
The directory on the iWay server where files are saved. You must specify a directory path only if the Payload Type parameter is set to Signal. |
|
Remove locally stored files |
If set to true, the FTP listener deletes the file stored locally after it is processed. This parameter requires a directory path to be specified for the Local Store Directory parameter. |
|
Pending Queue |
The directory to hold documents which are to be retried later. |
|
Suffix In Filter |
This limits input files to those with these extensions. For example, enter "XML,in" to accept files with extensions "xml" and "in". Note that this is not case-sensitive. Do not use a period (.), use a dash (-) to mean no extension, or an asterisk (*) to mean any. |
|
Duration |
The maximum time that a document can remain in the retry pending queue. |
|
Retry |
The interval between retrying pending requests |
|
Do not unzip ZIP files |
This passes ZIP files as a single file for processing (requires ACCEPT FLAT turned on). |
|
Bad File List |
This maintains a list of files with errors, preventing them from being re-accessed. If set to true, the files will not be retried. |
|
Delete After Read |
This determines whether to delete the file after it is read. If set to true, the file is deleted by the listener. If set to false, the file will not be deleted by the listener. |
|
File Protect |
This emits a temporary name and then renames it to the desired name. |
|
Security | |
|
User Name |
The user ID on the SFTP server. |
|
Password |
The user password on the SFTP server. |
|
Private Key |
The path to the private key file for public-key authentication. |
|
Passphrase |
The passphrase used to protect the Private Key |
|
Other | |
|
Whitespace Normalization |
Specifies how the parser treats whitespace in element objects. Select preserve (default) to turn off all normalization as prescribed by the XML Specification. Select condense to remove extra whitespaces in pretty printed documents and for compatibility with earlier versions. |
|
Accepts non-XML (flat) only |
If set to true, the listener expects flat (non-XML). Automatic parsing is not performed. |
|
Optimize Favoring |
Use this when the selection of memory is useful for large input document |
|
Multithreading |
The number of documents that can be processed in parallel |
|
Execution Time Limit |
The time limit for document execution (in seconds) before it is cancellation is attempted. (Also see system property kill interval. This applies to agent stacks and sets a lower limit for process flows.) |
|
Polling Interval |
The interval at which to check for new input |
|
Default Java File Encoding |
The default encoding if incoming message is not self-declaring (that is, XML) |
|
Agent Precedence |
This changes the order by which the engine selects agents. Normally the document overrides the listener. This is used to manage iWay documents |
|
Always reply to listener default |
If set to true, the default reply definition is used in addition to the defined replies |
|
Error Documents treated normally |
If set to true, the error documents will get processed by any configured pre-emitters |
|
Listener is Transaction Manager |
If set to true, the agents run within a local transaction managed by the listener |
|
Record in Activity Log(s) |
If set to true, the activity on this channel will be recorded in the activity logs. If set to false, the activity will not be recorded. |
Note: The SFTP listener supports streaming. Streaming is used for large documents or documents for which the application needs to split the input into sections under the same transaction. For more information on streaming and configuring streaming preparsers, see the iWay Service Manager Component and Functional Language Reference Guide.
The following table lists and describes the special registers (SREGs) available on the SFTP listener.
|
Name |
Level |
Type |
Description |
|---|---|---|---|
|
iwayconfig |
System |
String |
The current active configuration name. |
|
msgsize |
Document |
Integer |
The physical length of the message payload. |
|
name |
System |
String |
The assigned name of the master (listener). |
|
protocol |
System |
String |
The protocol on which the message was received. |
|
source |
Document |
String |
The full name of the input file. |
|
tid |
Document |
String |
Unique transaction ID. |
-
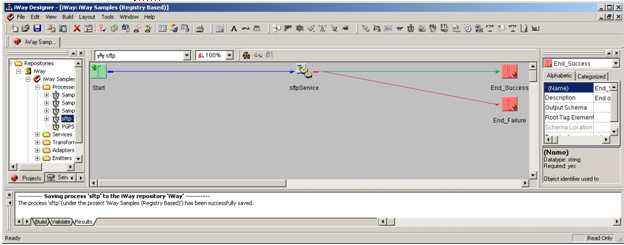
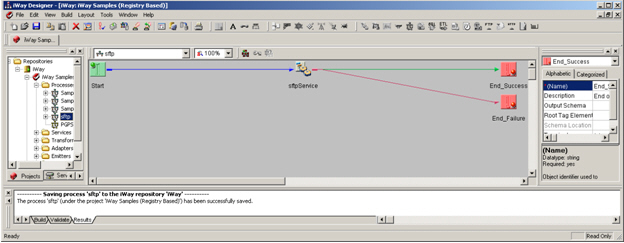
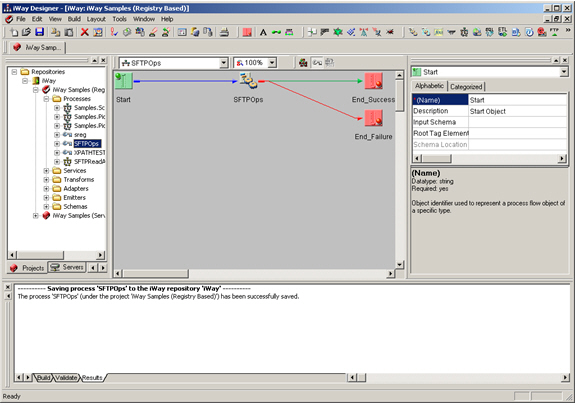
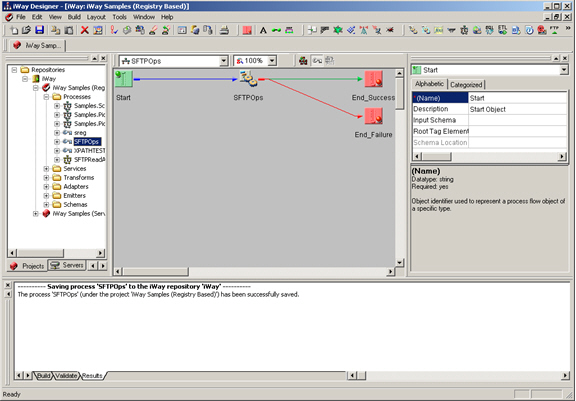
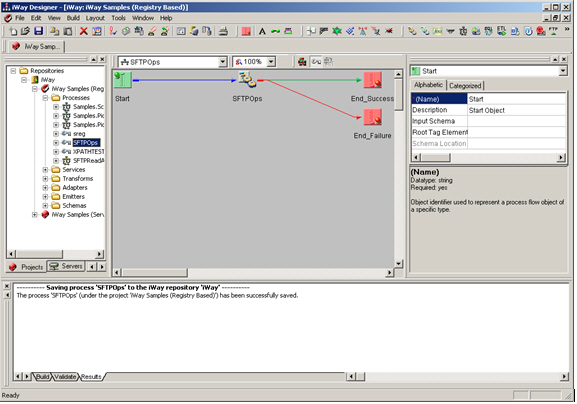
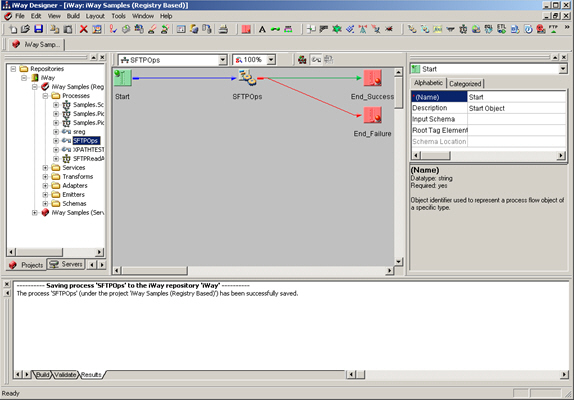
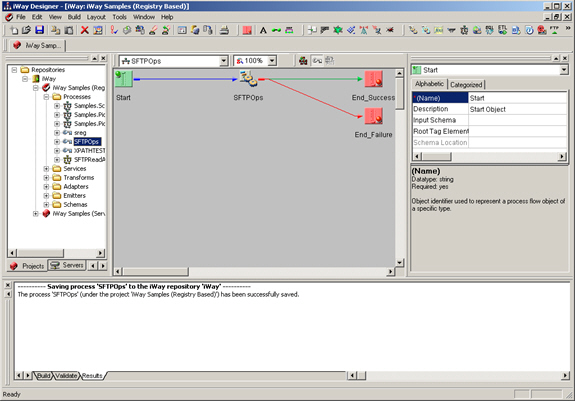
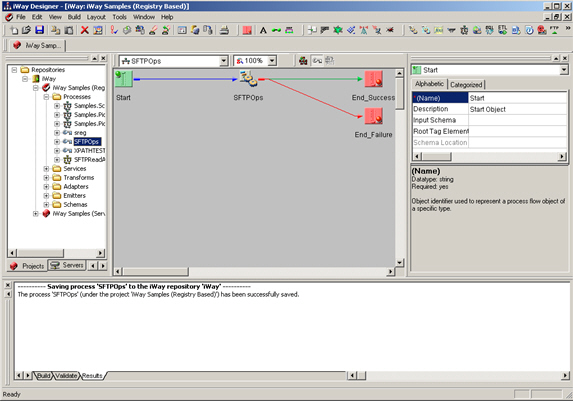
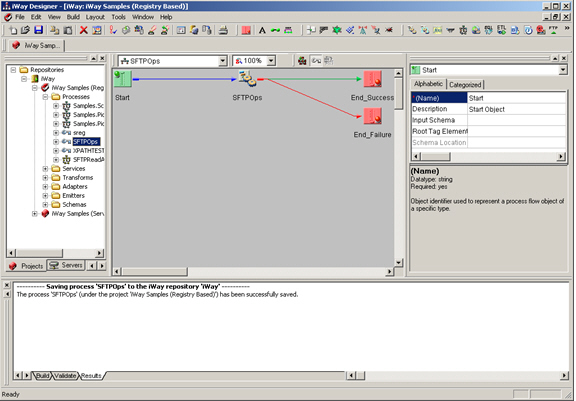
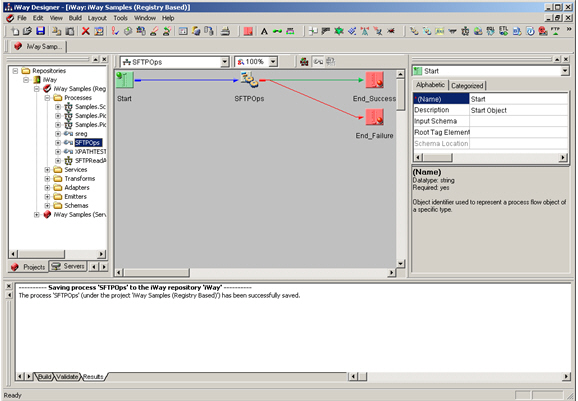
Construct an inlet consisting of an SFTP listener as shown
below:
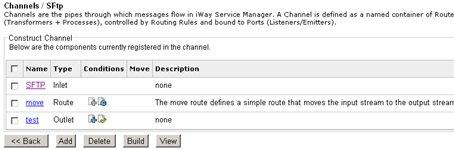
-
Construct a channel (for example, mySFTP) consisting of the
inlet, move Route and a File emitter which writes the output file
to a test directory (for example, c:\test).
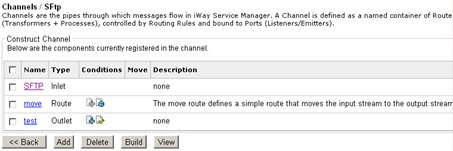
- Build and deploy the channel.
- Start the channel.
- Place an XML file in the /home/org directory on the SFTP host using SFTP commands, or if the server is a Windows machine, by copying it to the folder.
- The SFTP channel processes this message and drops the file into the c:\test directory on the iway client machine.